Certificate Expiration Dashboard
The Certificate Expiration Dashboard (cert-check.itsec.tamu.edu) is a tool that allows Technology Services employees to monitor subdomains (or hostnames of subdomains) belonging to tamu.edu for certificates that will be expiring within a given range.
An example of a subdomain of tamu.edu would be security.tamu.edu.
A query to a subdomain will include all certificates registered hostnames belonging to that subdomain expiring within the given expiration period, including certificates that have that subdomain listed in its Alternative (DNS) Names.
A hostname of a subdomain would be, for instance, docs.security.tamu.edu.
A query to a hostname will (generally) only return a specific certificate, unless multiple certificates have been issued.
This tool queries publicly-available data from Certificate Transparency Logs (CTL) to show what certificates registered to the tamu.edu domain are about to expire, and what CA they are registered with.
You can use this tool to look up certificate expiration dates for subdomains of tamu.edu and subscribe to get email notifications when new certificates enter an expiration range.
Examples
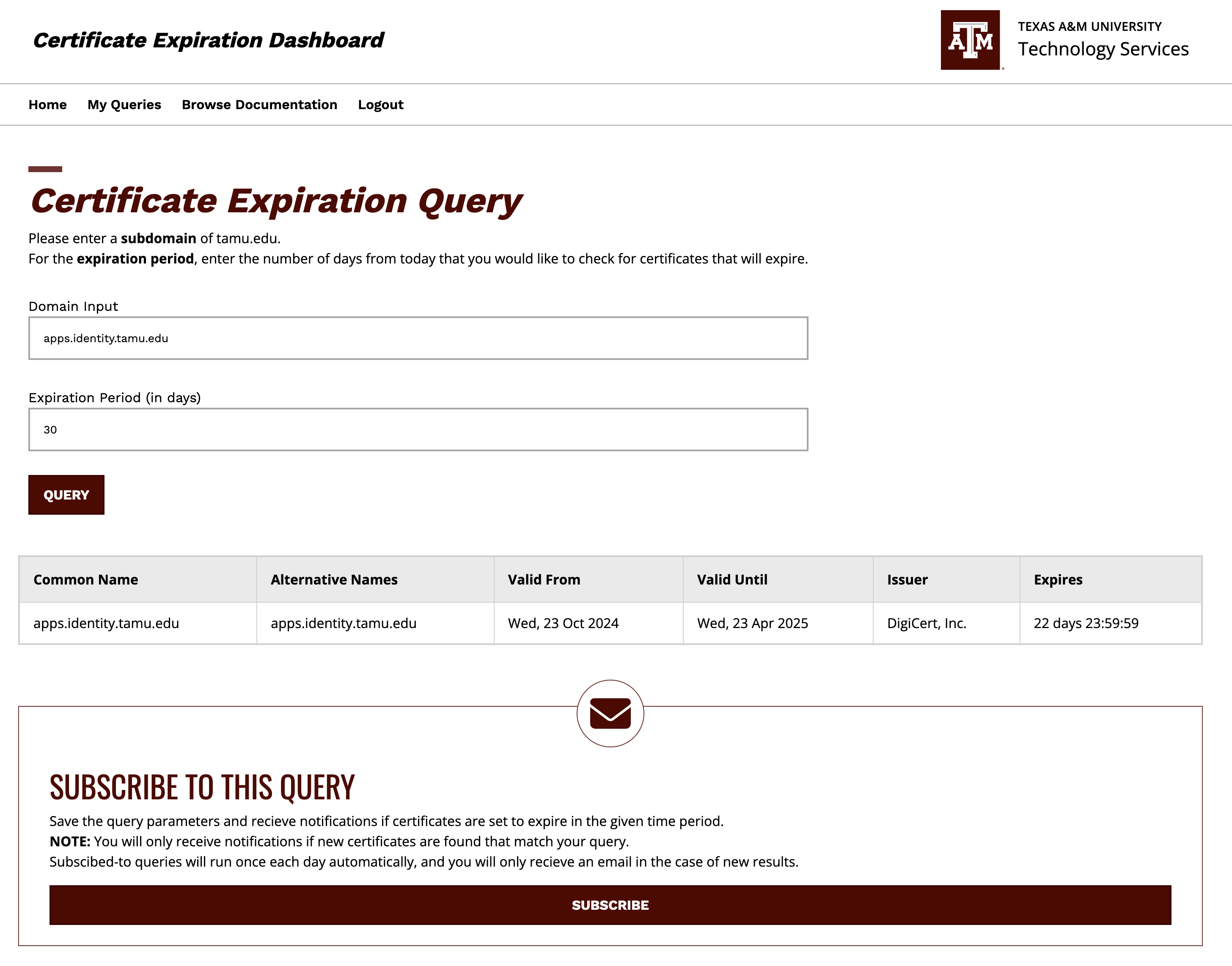
- Joe Aggie is a Technology Services employeee in charge of the tool hosted on apps.identity.tamu.edu, and is interested in making sure the site doesn't become unavailable due to an expired web certificate.
- Joe enters
apps.identity.tamu.eduinto the "Domain Input" field, along with30in the Expiration Period, and sees a result showing that the certificate in question is expiring within 22 days.- If he instead sees no results, this means that there are no certificates set to expire within the given Expiration Period.
- Joe subscribes to the query
apps.identity.tamu.eduwith an expiration window of5days, and then later recieves an email notification when the Let's Encrypt certificate is 5 days away from expiring.
- Joe enters
An example of a query to a particular hostname looks like this:
- Joe Aggie is an Associate VP interested in monitoring all certificates within his department's subdomain
it.tamu.edu.- Joe enters
it.tamu.eduinto the "Domain Input" field, along with15in the Expiration Period, and hits the 'Subscribe' button- every day that a new certificate belonging to a hostname of
it.tamu.eduenters the expiration window, Joe will get an email notification listing every non-expired certificate within that window.
- every day that a new certificate belonging to a hostname of
- Joe enters
An example of an email notification looks like this:
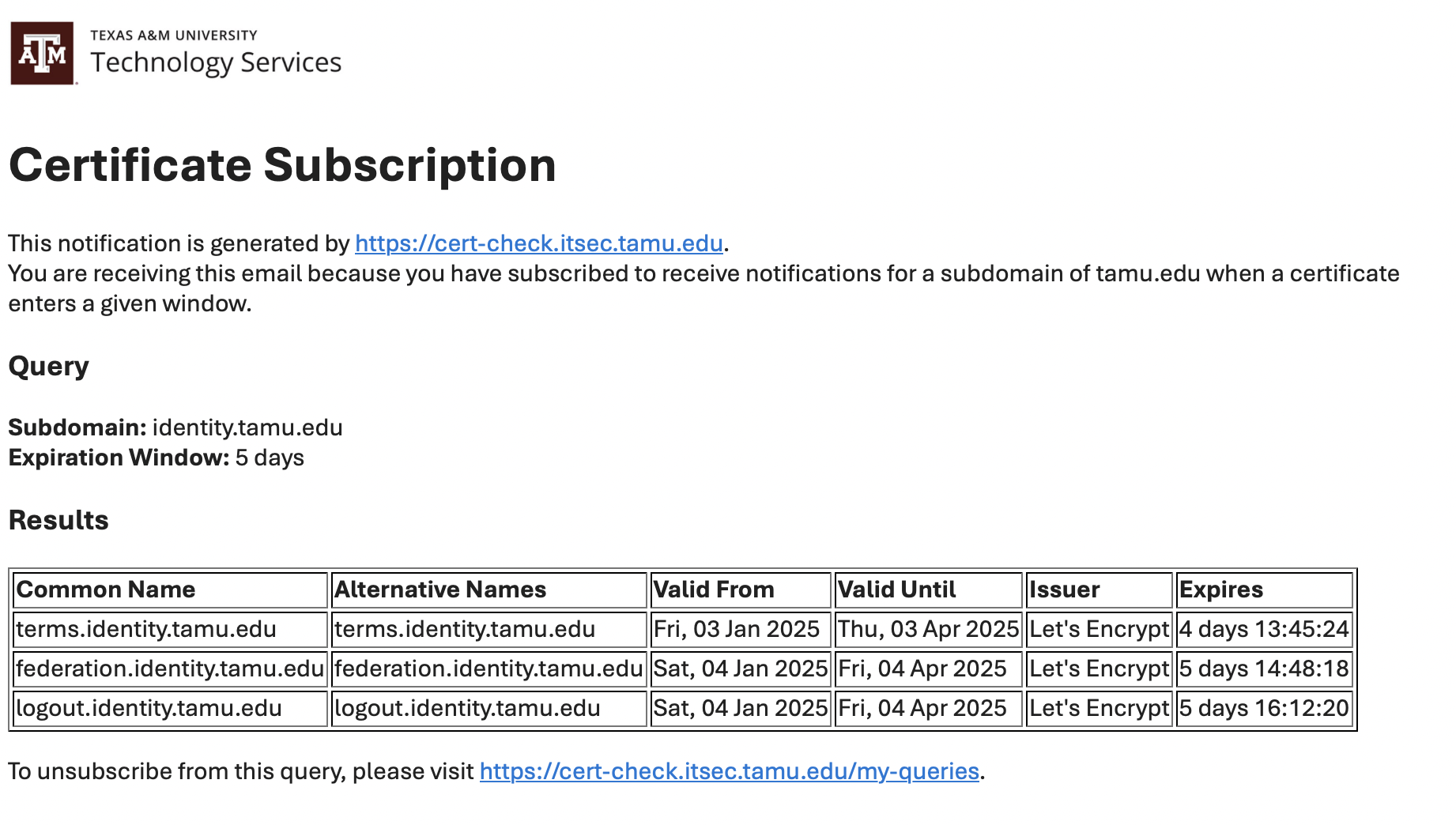
For subscribed queries, users will recieve email notifications once per day if there is a new certificate entering the expiration window they are interested in.
In the case that no new certificates have entered the given expiration range, users will not recieve an email.
Users will get a confirmation email when subscribing to a new query, and can manage their subscriptions in the My Queries page.
Notes
If a query has been searched for in the last day, the external results will be stored on a local cache database and will be fetched quickly. As a function of subscribing, saved queries will be re-run once a day and checked for new certificates, and a result of that is subscribed-to queries should be generally available in the local cache.
However, if a query has not been searched for within the last day, this tool will query the external data sources, which can take a varying amount of time.
Please allow up to several minutes for the results to fetch for fresh queries.
The data sources ingested by the Certificate Expiration Dashboard are provided free to the public on a "Best Effort" basis, with no Service Level Agreement (SLA).
Please note - There may be temporary service outages from time to time that impact the ability of the tool to gather information from these data sources. This usually is a result of high public demand on these third-party data sources.